|
May/June 2009 | Volume 1/Number 3
Eye on the Money
What Operators Must Do To Participate in Emerging Revenue Sources By Grant Lenahan
This is the third in a 7-part series that looks at how our industry will change, survive and, in fact, grow as we transition from our various historical roots to the future that will be powered by NGNs. Consequently, this month we’ll look at what I believe to be the only logical question: “So, how can we make money on those?” This is a particularly good question since nearly all content, advertising and commerce originates with third parties. In fact, the world already has an excellent “existence proof” called the World Wide Web. In that model, content owners and content retailers provide all the content and services and our industry provides the dumb pipes. In other words, we are cut out entirely, and receive zero revenue from the cornucopia and its associated global trillions. One definition of insanity is repeating the same action and expecting a different result. Previous forays resulted in the proverbial “dumb pipes.” How can we avoid having history repeat itself? Fortunately, it turns out, consumers and e-commerce retailers don’t like the outcome much more than we did. And, neither do the original architects of the Internet. Finally, in a perfect storm, they all largely agree on the drawbacks of the “over the top” model. Their words are slightly different, but they tell a remarkably similar story. Follow it, and we have a blueprint for how communications carriers might add value and insert themselves into the middle of the content–advertising–information–commerce value chain. So, let’s look at this data. Some of the best data comes from the OECD (Organization for Economic Co-operation and Development). It is especially powerful, because they polled both consumers and merchants and, therefore, can see the similarities in what each wants. Figure 1 summarizes the reasons that some consumers do NOT shop online. 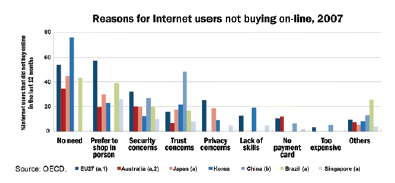 In a nutshell, they are concerned with security, privacy, difficulty (complexity of the process) and often don’t have a suitable payment method, such as a major credit card. These are all problems that communication service providers (CSPs) can solve or help to greatly reduce — it’s the value-add that is needed to avoid the dumb pipe scenario. Merchants voiced similar concerns. The OECD data for merchants is shown in Figure 2 and can also be summarized as concerns over security, trust, technology/complexity, and payment methods. But surely, these must be the outliers. The Internet has proven itself a fabulous vehicle for innovation. These are just bumps in the road that will be overcome in time, right? 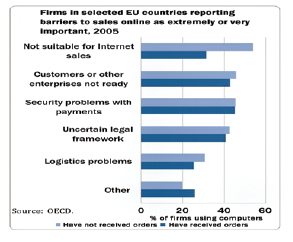 Well, yes, I suppose so. But overcome how?… and by whom? In January of 2006, This is good news. CSPs have strong infrastructure to authenticate users, beginning with things like mobile Subscriber Identity Module authentication and physical loop ID. Moreover, they also have infrastructure to handle transactions, micro and macro charges, separations, settlements, limits, authorizations, ad delivery and context identification(such as where you are and what content you are requesting). A value proposition is emerging. One based on becoming the authentication, authorization, personalization and charging proxy for many online services and merchants. No more giving credit card numbers to unknown merchants or sharing personal data without approval. No more sending adult material to children. Enter the age of “enter once, use many”. Less typing and updating into notoriously different and inscrutable web site formats. Classic management theory teaches to invest in core competencies — things that will enable differentiation — and to outsource common functions to the best, lowest cost supplier. Auto makers buy bearings, tires and glass but do their own styling and motors. Given the choice — e-merchants will likely do the same, paying CSPs to perform these commodity functions for them — and do a better job at it along the way. There’s a simple beauty to this vision. Network companies do what they do best: secure, complex, high-scale transactions on a more intelligent network. A smart pipe. Grant F. Lenahan is Vice President and Strategist, IMS Service Delivery Solutions at Telcordia Technologies, Inc. For more information, visit www.telcordia.com. NGN Magazine Table of Contents |