
Of late, terms like "big data" and "AI" have taken the internet by storm. This fervor is becoming contagious as more companies try to figure out how to use these technologies to improve their product. Big data and analytics are impacting every sector of the modern economy, and the security sector is no different. Analytics holds great promise for assisting ongoing enterprise efforts to spot anomalies and stop security lapses and cyberattacks before they can compromise systems and engage in malicious activity or, at the very least, before too much harm is done.
This article takes you through the different dimensions of security analytics and how you can make the most of it for informed data security decisions.
What Is Security Analytics?
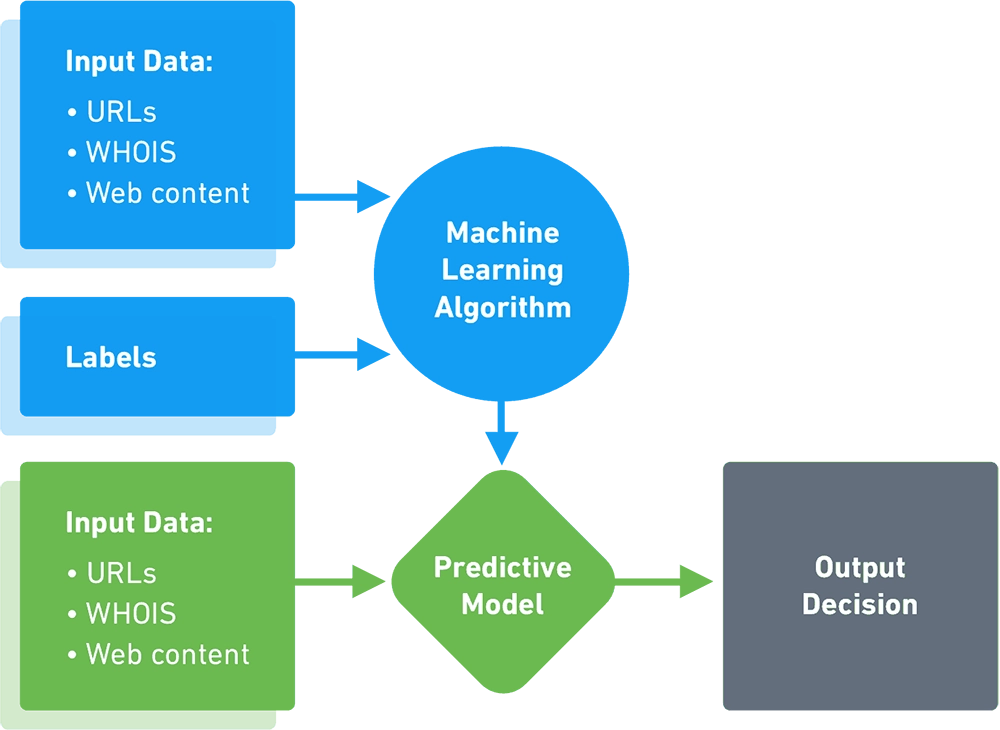
In simple terms, security analytics is the process of collecting, analyzing, and interpreting security-related data from various sources with the goal of detecting, preventing, and responding to security incidents. To give businesses a more complete picture of their security posture and to assist them in promptly identifying and responding to security risks, this field integrates parts of conventional security methods with data analysis, machine learning, and other cutting-edge approaches.
Use Cases for Security Analytics
Before jumping to the know-how of utilizing security analytics, it is important to know its use cases and capabilities. This will provide you with a better picture of the different methods of incorporation and give you an idea of how to make the most of them.
Security analytics has a wide range of capabilities that helps organizations in effective data security posture management and threat mitigation.
The main benefit of security analytics is threat detection. The primary purpose of security analytics is to detect threats ahead of time. This can be done by analyzing logs, network traffic, and other data for patterns and anomalies to detect malicious behavior.
Further, organizations are required to comply with regulations and other conditions, which may update on an ad-hoc basis over time. Security analytics can help organizations monitor their systems and networks to ensure they are in compliance with the necessary requirements.
Using security analytics, networks and endpoint devices can also be watched for indicators of compromise, such as malware infections or illegal access, which helps enhance overall network and endpoint security.
Additionally, machine learning and other cutting-edge methodologies can be used in security analytics to study user behavior and spot odd trends that might point to malicious activities. Data transfers, unusual login attempts, and other actions that depart from customary behavior all fall under this category.
Obstacles in Security Analytics
As many benefits as it may provide, security analytics is sometimes a steep hill to climb as it comes with its own set of challenges. Nevertheless, companies need to overcome these hurdles to reap the benefits of security analytics, as they are significant. So, what are these roadblocks that one must be aware of?
Organizations frequently struggle to manage and make sense of the enormous amounts of data (data overload) from various sources that security analytics relies on. Additionally, due to information saturation, it may be challenging to pinpoint the most significant security events.
Additionally, security analytics needs to be connected with your company's existing systems to provide a complete picture of your organization's security posture. This is a problem as most companies use a variety of security tools and technologies.
Another challenge of using security analytics is the risk of false positives, where a security incident is mistakenly identified as a threat. This can lead to wasted resources and time, as well as an increased risk of real security incidents going undetected.
Organizations must also consider the expenses of investing in security analytics against the advantages because it can be a difficult and expensive technology to adopt and maintain.
When it comes to privacy, sensitive data is frequently collected and analyzed for security purposes, which can cause privacy issues and complicate regulatory compliance. To protect sensitive data, organizations need to ensure they are in compliance with privacy laws and regulations and that they have strong security measures in place.
Utilizing Security Analytics for Informed Data Security Decisions
Now that we've got a heads-up on what security analytics is, its capabilities, use cases, and downsides, let us look at how to utilize analytics for making sound data security decisions.
One should start with defining goals and objectives. Prior to adopting security analytics, it's critical to establish the program's aims and objectives in detail. This will make it more likely that the appropriate data will be gathered, processed, and the findings will be in line with the organization's overall security policy.
Once the goals are jotted down, the next step involves choosing the right sources of data. Security analytics requires data from various sources, including logs, network traffic, and other security-related devices and applications. It is important to choose the right data sources that will provide the most valuable information for the organization's specific needs.
Further, quality data helps you to better implement advanced analytics techniques. For example, organizations can improve their entire security posture and find relevant patterns and connections in the data by utilizing machine learning, statistical analysis, and other advanced methodologies.
The penultimate step is to validate the results. Validating results helps in asserting the accuracy of the information and that the desired results are being accomplished. This can be done via manual reviews, regular testing, and tuning of the analytics algorithms.
Lastly, it is recommended to collaborate with stakeholders to guarantee that security analytics is in line with the broader company strategy and that the results are used to make sensible decisions about data security. Thus, businesses must closely collaborate with all stakeholders, including IT, security, business, and regulatory groups.
Conclusion
With the increase in attacks and complex threat environments, it is getting more difficult for organizations to maintain their security infrastructure. Fortunately, security analytics can help navigate these complex threat environments. By aggregating, correlating, and analyzing the data, it is possible to foresee and mitigate emerging attacks well before any sensitive data is compromised.
