2020 undeniably brought about many unprecedented challenges. Due to the global pandemic, political unrest, and raging wildfires, other less-tangible events fell to the wayside. A stark rise in cybersecurity attacks was one such challenge which, according to a range of sources, made 2020 a record-breaking year for data loss, data breaches and the overall volume of cyber-attacks.
Many of these attacks can be attributed to the forced shift to remote work, where companies were required to quickly pivot their operations almost overnight. However this was not the sole cause. In fact, the majority of these costly attacks were due to the overall poor state of business and personal cybersecurity readiness, with only 5 percent of files adequately protected across the majority of businesses. Unfortunately, this lack of protection has proven to be costly, with the average cost of a data breach in 2020 sitting at close to $4 million dollars.
While cybersecurity can often feel like a game of catch-up, especially in terms of selecting and implementing the most up-to-date software and security measures, it doesn’t have to be. New platforms have recently begun to emerge which completely change the landscape of cybersecurity. Smart Eye Technology is one such platform, with their groundbreaking offering not only protecting users from cybersecurity risks, but also from ‘over the shoulder’ data leaks.
New and Unique Security Methods
Recently available on the Samsung (News - Alert) AppStack Marketplace, Smart Eye Technology helps companies protect the privacy and security of confidential information through their biometric-based file sharing platform on both desktop and mobile operating systems. Files regularly shared between employees, customers or vendors are secured through their proprietary self-protecting data technology which encrypts data in transit and only allows opening through the unique biometric signature of approved users. This signature is made up of a combination of facial features, fingerprints, print behavior, as well as voice recognition to ensure only the true recipient is able to access protected files.
For an added level of security, each company is empowered through Smart Eye to create their own ‘private pond’ for both internal and external collaboration. This means for anyone to recieve or share files through the platform, the system administrator must approve them first. This tactic, which essentially locks confidential information by shutting out all others, protects against wire fraud, compromised emails and both intentional and unintentional data leaks from employees.
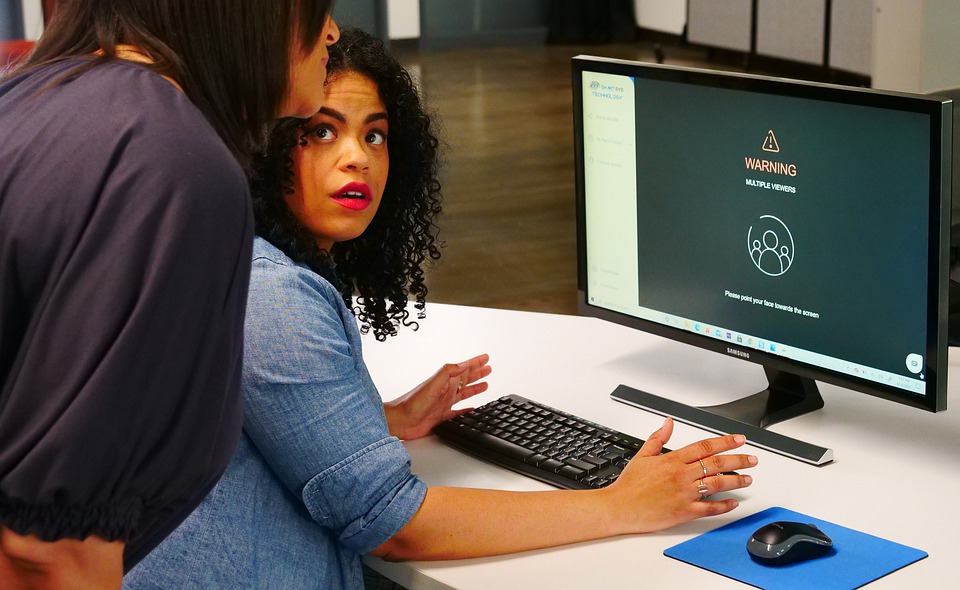
Additionally - and unique to Smart Eye Technology - the platform also protects from in-person, ‘over the shoulder,’ data breaches through the same biometric security measures. This means that if an unauthorized person is looking at the screen, either when the authorized party has stepped away from their device, or over the authorized parties’ shoulder when a protected file is being viewed, it will automatically lock to protect the confidential information.
Stronger Controls Meets Layered Security to Provide the Ultimate Protection
It’s well-understood by IT professionals that there is no single way to protect a business from malicious attacks. As such, the key to providing the most effective protection is to layer different types of security measures so any gaps or loopholes are significantly smaller. According to the Identity Management Institute, the three layers of any effective IT security system are prevention, detection and response.
Smart Eye Technology fulfills each of these security objectives by; Preventing access to confidential information by unauthorized parties via layered biometric authentication protocols, their ‘private pond,’ and proprietary self-protecting data encryption technology; Detecting unauthorized access through real-time authentication; and responding to threats by locking confidential files when unauthorized access is detected.
In addition to their flagship features, the technology also empowers additional control and extra layers of security by enabling time-limit access on files, activity tracking, and instant access termination. Each of these features, as well as all system activity is easily monitored via a control panel, which enables administrators to monitor the security of files in real time. Their biometric capabilities also enable identity-verified e-signatures, which ensures only the intended user can sign a contract. This offers extra protection in legal disputes because this function provides solid proof of which parties signed a document or contract, backed up by biometrics.
Although sourcing and implementing the right cybersecurity technology is often an intimidating prospect, it’s also vital for the protection of sensitive data. With business reputation and significant financial loss at stake, platforms like Smart Eye Technology not only adds layers of protection to secure sensitive data in the cyber realm, but in the physical world as well.
